RESOURCES
Templates, Forms, & FAQ's
Insight Templates & Forms
Frequently Asked Questions
Insight Templates & Forms
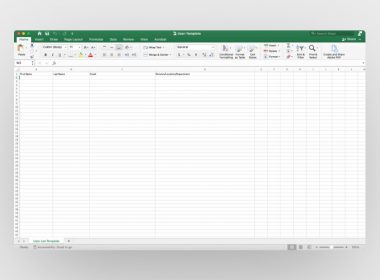
Insight Excel User Template
Download our Microsoft Excel template to format your user lists
Insight Templates & Forms
DOCUMENT DOWNLOADS:
Frequently Asked Questions
Contact Information
Who can I contact for answers to technical or program related questions?
John Bomba
Senior Security Engineer
Email: jbomba@d2cybersecurity.com
Phone: 732.507.7341
Who can I contact for answers to administrative questions or for more information on D2’s Cyber Loss Control Services?
Brian Lau
Director
Email: BrianLau@d2cybersecurity.com
Phone: (609) 915-2758
Whitelisting
How do I whitelist D2 Cybersecurity emails & domains
Emails that come from our phishing campaigns may get blocked by your spam filters. To avoid this, please have your IT administrator whitelist the following domains so that the phishing emails sent can be delivered to target users throughout your organization.
mailsupportsystems.com
trackingsupportservices.com
payrollsupportadmin.com
emessageadmin.com
messageservicesadmin.com
helpdesksupportgroup.com
The domains above are registered to the following IP Addresses:
104.37.180.1
162.245.189.76
How do I customize spam filter settings for my email
G Suite: Create and approved sender list: Click here for official G Suite Documentation
Microsoft Office 365: Configure 3rd Party Phishing Simulations: Click here for official Microsoft documentation.
Please note: Microsoft does not recommend using transport rules for phishing simulations.
Microsoft Defender for Office 365: How to configure anti-phishing policies in EOP. Click here for official Microsoft documentation
Phishing
What do D2’s phishing simulation emails look like?
Our phishing simulations closely resemble emails that you receive on a regular basis. They are created to look very similar to those sent by large, well-known corporations (i.e., Google, Amazon, Chase, etc.).
Who can I contact for answers to administrative questions or for more information on D2’s Cyber Loss Control Services?
Brian Lau
Director
Email: BrianLau@d2cybersecurity.com
Phone: (609) 915-2758
How do you decide the type of phishing simulation each client receives?
New email templates are carefully created and selected for each client and phishing period. Factors such as the time of year, client type (i.e., town vs. school), and location are all taken into consideration when we design our simulations.
Where do the email URLs link to?
All URLs within our phishing simulation emails link to D2’s own training domains. Upon clicking one of these links, the victim is sent to a landing page site that provides education on how they could have identified the simulated phishing attempt and how to avoid clicking on potentially malicious URLs in the future.
How long does each simulation take?
Phishing simulations normally run for one to two weeks, Monday through Friday.
Are users who don’t click the links affected?
Users that receive our simulated phishing emails will not be negatively impacted in any way.
Can I use my personal email for the phishing simulations?
No. We can only use an email address provided by your organization.
How do I add or remove users?
You can add/remove users (one at a time or in bulk) by uploading a list through our online portal here.
To ensure that all users receive the simulated phishing emails, please confirm that there are no typos on your list before submitting.
How often do you run these phishing simulations?
Our phishing simulations are run four times a year, once per quarter.
How will I know that the phishing simulation is coming from D2?
D2 will always send you test phishing simulations several days to a week in advance. The emails will be titled “D2 Cybersecurity Test”, and each will include a short message informing you of your upcoming campaign.
If you are still uncertain, please contact D2 for confirmation.
What should I do if I find an actual phishing attack?
Follow your organization’s policies for reporting a phishing attack.
Do not click anything in the email message.
Please contact D2 so that we may confirm the message’s legitimacy and help keep your school/municipality safe.
What should I do if the phishing simulations are getting blocked by my firewall/email filters?
See our whitelisting FAQ
Gap Assessment
What is a Gap Assessment?
The purpose of the Gap Assessment is to identify current gaps in your cyber security controls and practices against an industry recognized and established framework relevant to your vertical.
What is involved in a Gap Assessment service?
Once you participate in the service, the following process ensues:
- A welcome email is sent to your IT and Business Adminstrator Point of Contact (POC) to access the secure Insight portal.
- An online questionnaire will be accessible for each POC by logging into the Insight portal.
- Once the answers are submitted online in its entirety, a review or audit will happen.
- A final report with findings and recommendations will be prepared and available for you to download from the secure Insight portal
Self-assessment questionnaire: Who should answer what
The self-assessment questionnaires are divided into 2 parts based on your roles and responsibilities.
Answer the Administrator questions, if you’re responsible for:
- Vendor management and audit,
- Communication and press communication,
- Defining policies, procedures, and guidelines,
- Coordinating the Request for Proposals (RFP),
- Arranging security awareness training
- Assessing security risk and working with Cyber Insurance
- Authority to invoke incident response and disaster recovery process
Answer the IT questions, if you’re responsible for:
- Network and infrastructure management
- Implementing physical and technical safeguards for policies & procedures
- Configuration, inventory, and account management
- Scanning, patching and remediation of systems and applications
- Managing access to network, systems, and accounts
- Backup and recovery of data to comply with regulatory requirements
- Incident reporting, logging, analysis, and documentation
Can the questionnaires be answered by a single individual?
The questionnaire consists of two parts:
- Administrative – questions and controls that are relevant to administrative functions.
- Technical – questions and controls that are relevant to information technology functions.
The individual responsible for each of these functions within your organization should answer the associated section of the questionnaire. If a single individual is responsible for both of these functions, they may answer both sections.
Do I need to complete both parts?
Both parts of the questionnaire need to be completed online and submitted using the secured Insight portal.
Will my answers be audited?
Depending on the kind of service you’ve prescribed, your answers to the online questionnaire:
- Gap Assessment Lite – will be reviewed by our auditor without you and final report provided
- Gap Assessment Full – will be audited by our auditor with both IT and Administrator POC
How long are the reports available in the secure portal?
The report can be accessed and downloaded for the duration of the service contract. For multi-year contracts, historical reports can be accessed should one decide to undertake the service in subsequent years.
Vulnerability Assessment
How is confidential data handled?
No data will ever be downloaded or modified.
How do I customize spam filter settings for my email
G Suite: Create and approved sender list: Click here for official G Suite Documentation
Microsoft office 365: Configure 3rd Party Phishing Simulations: Click here for official Microsoft documentation.
Please note: Microsoft does not recommend using transport rules for phishing simulations.
Is D2 installing software on our systems during a vulnerability scan?
D2 will never install software on your systems during a vulnerability scan.
What IP address ranges will the various tests and scans originate from?
Vulnerability scans: 72.236.151.0/24
Will we have to whitelist the D2 source IP addresses?
There may be rare instances where D2’s IP addresses will need to be whitelisted.
D2 will reach out to the technical POC if this becomes necessary.
What happens if we forgot to include or would like to remove an IP that is on our initial KYC form?
Reach out to John Bomba to update your IP addresses.
John Bomba
Email: jbomba@d2cybersecurity.com
Phone: 732-507-7341
Additional IP addresses can be added at any time.
How does vulnerability scanning and penetration testing differ?
Vulnerability scanning uses automated tools to detect vulnerabilities in your network. During this process, the vulnerabilities are only detected, not exploited to gain access/control.
Penetration testing is a manual process that involves exploiting vulnerabilities, emulating what a hacker might attempt in an effort to access and take control of your network.
Will scanning affect my network performance/speed/backups?
Vulnerability scanning is usually completed in under an hour and is performed during off-hours to minimize the already small chance of it affecting your network.
We only use one IP address in our range of addresses. Should D2 scan only the address in use?
We recommend that ALL IP addresses be tested. Including those which are thought to be unused.
One of our goals is to identify potentially forgotten internet connected devices that might compromise the security of your network.
Can I request a specific window for a Vulnerability Scan/ Penetration test?
The KYC form has a “Testing Window” section or you can email John Bomba at jbomba@d2cybersecurity.com to modify the time you initially indicated.
Can we declare certain network resources off limits?
The KYC form has an “Exceptions” section. Reach out to John Bomba to update it, if needed.
Should we exclude Police Department IP addresses from vulnerability scanning?
Our advice is to scan every external IP address to detect any vulnerabilities. Leaving a critically important section of the network unscanned/tested might leave it vulnerable to a cyber-attack that could have otherwise been prevented.
D2 will NOT conduct a vulnerability scan on any interconnected systems.
D2 will NOT attempt to connect to any interconnected county, state, or federal systems.
Only the IP addresses listed on the KYC form will be included.
What kind of vulnerability scan reports will I receive?
Reports will be available as downloadable PDF’s at https://insight.d2cybersecurity.com/
When can I expect to receive a report?
Your report should be available the next business day after the scan is performed, usually the day after the KYC form is submitted.
Can my reports be emailed to me?
No. Due to the sensitive nature of the information in the vulnerability reports they can only be access through the insight portal. https://insight.d2cybersecurity.com/
Can I share my Insight login credentials?
We strongly advise that you DO NOT share your Insight login credentials (or share credentials for any other systems that you might need to access).
If you would like to add more than two POCs, please either provide an additional copy of the KYC form that includes the additional users’ information or contact John Bomba.
How are vulnerabilities classified?
Vulnerabilities are classified on a scale of Low, Medium, High, and Critical, based on their CVSS score.
What happens if a Critical vulnerability is detected?
In the event that we find a Critical vulnerability, D2 will notify the POCs within one business day.
My report is blank and only displays a D2 logo. What does this mean?
This means that our scans did not detect any vulnerabilities at this time.
Please keep in mind that new vulnerabilities and exploits can be found daily, so you may see something appear on the next report.
What should I do with my reports?
If a vulnerability or exploit has been identified, D2 will include any known remediation steps within the report. We advise that you discuss these suggested solutions with your technology POCs.
What IPs should I provide for Vulnerability Scanning & External Penetration Testing?
Vulnerability Scanning and External Penetration Testing are conducted against your public IPs and domains. Please keep in mind the private IPs in the ranges listed below are not valid IPs for those services:
- Class A: 10.0. 0.0 — 10.255. 255.255
- Class B: 172.16. 0.0 — 172.31. 255.255
- Class C: 192.168. 0.0 — 192.168. 255.255
We have a range of IPs but only use 2 of them. Should we limit the scanned IPs to those 2 or include the entire range?
Include the entire range. This will ensure if you add a host on to an IP in the future it will automatically be included in the scans and it will also ensure that if there are any “rogue” devices connected to your network the are similarly scanned.
Our firewall admin panel is only accessible from inside our network but the IP is public should we scan it?
Yes the firewall may still respond to certain queries and some vulnerabilities can still be detected. It’s important to verify that all security patches are up to date and configured properly. Vulnerability scanning can assist with that.
What is the difference between a public and private IP address?
In general, any IP that is on the following list is a private IP used inside a network/firewall and not suitable/reachable for external scans:
- 10.0. 0.0 to 10.255. 255.255
- 172.16. 0.0 to 172.31. 255.255
- 192.168. 0.0 to 192.168. 255.255
Please keep in mind there are others such as 127.0.0.1 that are special addresses that would also be unacceptable for external vulnerability scanning. see https://en.wikipedia.org/wiki/Reserved_IP_addresses
Penetration Testing
How is confidential data handled?
No data will ever be downloaded or modified.
How do I customize spam filter settings for my email
G Suite: Create and approved sender list: Click here for official G Suite Documentation
Microsoft office 365: Configure 3rd Party Phishing Simulations: Click here for official Microsoft documentation.
Please note: Microsoft does not recommend using transport rules for phishing simulations.
Is D2 installing software on our systems during a vulnerability scan?
D2 will never install software on your systems during a vulnerability scan.
What IP address ranges will the various tests and scans originate from?
Vulnerability scans: 72.236.151.0/24
Will we have to whitelist the D2 source IP addresses?
There may be rare instances where D2’s IP addresses will need to be whitelisted.
D2 will reach out to the technical POC if this becomes necessary.
What happens if we forgot to include or would like to remove an IP that is on our initial KYC form?
Reach out to John Bomba to update your IP addresses.
John Bomba
Email: jbomba@d2cybersecurity.com
Phone: 732-507-7341
Additional IP addresses can be added at any time.
How does vulnerability scanning and penetration testing differ?
Vulnerability scanning uses automated tools to detect vulnerabilities in your network. During this process, the vulnerabilities are only detected, not exploited to gain access/control.
Penetration testing is a manual process that involves exploiting vulnerabilities, emulating what a hacker might attempt in an effort to access and take control of your network.
Will scanning affect my network performance/speed/backups?
Vulnerability scanning is usually completed in under an hour and is performed during off-hours to minimize the already small chance of it affecting your network.
We only use one IP address in our range of addresses. Should D2 scan only the address in use?
We recommend that ALL IP addresses be tested. Including those which are thought to be unused.
One of our goals is to identify potentially forgotten internet connected devices that might compromise the security of your network.
Can I request a specific window for a Vulnerability Scan/ Penetration test?
The KYC form has a “Testing Window” section or you can email John Bomba to modify the time you initially indicated.
Can we declare certain network resources off limits?
The KYC form has an “Exceptions” section. Reach out to John Bomba to update it, if needed.
Should we exclude Police Department IP addresses from vulnerability scanning?
Our advice is to scan every external IP address to detect any vulnerabilities. Leaving a critically important section of the network unscanned/tested might leave it vulnerable to a cyber-attack that could have otherwise been prevented.
D2 will NOT conduct a vulnerability scan on any interconnected systems.
D2 will NOT attempt to connect to any interconnected county, state, or federal systems.
Only the IP addresses listed on the KYC form will be included.
What kind of vulnerability scan reports will I receive?
Reports will be available as downloadable PDF’s at https://insight.d2cybersecurity.com/
When can I expect to receive a report?
Your report should be available the next business day after the scan is performed, usually the day after the KYC form is submitted.
Can my reports be emailed to me?
No. Due to the sensitive nature of the information in the vulnerability reports they can only be access through the insight portal. https://insight.d2cybersecurity.com/
Can I share my Insight login credentials?
We strongly advise that you DO NOT share your Insight login credentials (or share credentials for any other systems that you might need to access).
If you would like to add more than two POCs, please either provide an additional copy of the KYC form that includes the additional users’ information or contact John Bomba.
How are vulnerabilities classified?
Vulnerabilities are classified on a scale of Low, Medium, High, and Critical, based on their CVSS score.
What happens if a Critical vulnerability is detected?
In the event that we find a Critical vulnerability, D2 will notify the POCs within one business day.
My report is blank and only displays a D2 logo. What does this mean?
This means that our scans did not detect any vulnerabilities at this time.
Please keep in mind that new vulnerabilities and exploits can be found daily, so you may see something appear on the next report.
What should I do with my reports?
If a vulnerability or exploit has been identified, D2 will include any known remediation steps within the report. We advise that you discuss these suggested solutions with your technology POCs.
What IPs should I provide for Vulnerability Scanning & External Penetration Testing?
Vulnerability Scanning and External Penetration Testing are conducted against your public IPs and domains. Please keep in mind the private IPs in the ranges listed below are not valid IPs for those services:
- Class A: 10.0. 0.0 — 10.255. 255.255
- Class B: 172.16. 0.0 — 172.31. 255.255
- Class C: 192.168. 0.0 — 192.168. 255.255
Course Reminder Email
Why am I receiving this email?
Your organization has enrolled you in D2 Cybersecurity’s Cyber Awareness Education program, and you have not yet fully completed your courseware.
I’m having problems logging in.
Please refer to the link provided near the bottom of your reminder email for issues logging in (Having issues logging in? Click here). This link will help you reset your password. If you continue to run into issues, please reach out to support@d2cybersecurity.com to request a password reset, with the following information:
First Name:
Last Name:
Email Address that received the reminder email:
Organization:
How can I complete my courseware?
Once you have logged into your training account through the login link provided in your reminder email, you may view your course modules by clicking on “My courses” at the top of your screen. Both the course (SCORM Package) and Quiz must be completed to fully complete your courseware.